Archive for
Archive for
Start Your Verify Journey: 90 Minutes to an Identity Roadmap
IBM Verify & Identity Modernization In a world where identity is the new perimeter, organizations must move beyond brittle passwords and fragmented identity stacks. IBM Verify offers a unified identity platform that aligns with intiGrow’s mission: secure digital transformation that reduces risk, meets compliance, and enables business velocity. Why identity must be strategic Identity decisions ripple across security, user […]

Meet intiGrow at the Cybersecurity Summit Philadelphia – September 25, 2025
Don’t miss this opportunity to gain insights that could protect your organization from significant financial loss and reputational damage.
From Chaos to Control: Mastering Hybrid Cloud with Modern Infrastructure Management
Don’t miss this opportunity to gain insights that could protect your organization from significant financial loss and reputational damage.

Unlock Secure AI Workflows in the Cloud with HashiCorp and intiGrow
Don’t miss this opportunity to gain insights that could protect your organization from significant financial loss and reputational damage.

Beyond Onboarding: Why a Robust Identity Lifecycle is Your First Line of Defense Against Cyber Threats
Don’t miss this opportunity to gain insights that could protect your organization from significant financial loss and reputational damage.

Getting Identity Life Cycle Management Right: Key Considerations and Best Practices
Don’t miss this opportunity to gain insights that could protect your organization from significant financial loss and reputational damage.

Monitoring Your Vendor’s Cybersecurity Posture: IBM Solution Posture Management & Data Resilience Validation
Don’t miss this opportunity to gain insights that could protect your organization from significant financial loss and reputational damage.

How to Prevent a Cybersecurity Breach from a Former Employee’s Account
This breach serves as a stark reminder of the ever-evolving cybersecurity landscape. We must stay vigilant, continuously update our security practices, and educate our teams on the importance of cybersecurity hygiene. By following the key takeaways from this breach, you can prevent a similar incident from happening to your organization.
The Pros and Cons of Passwordless Authentication: A Comprehensive Analysis
Passwordless authentication offers a promising alternative to traditional password-based systems, providing improved security and a better user experience.

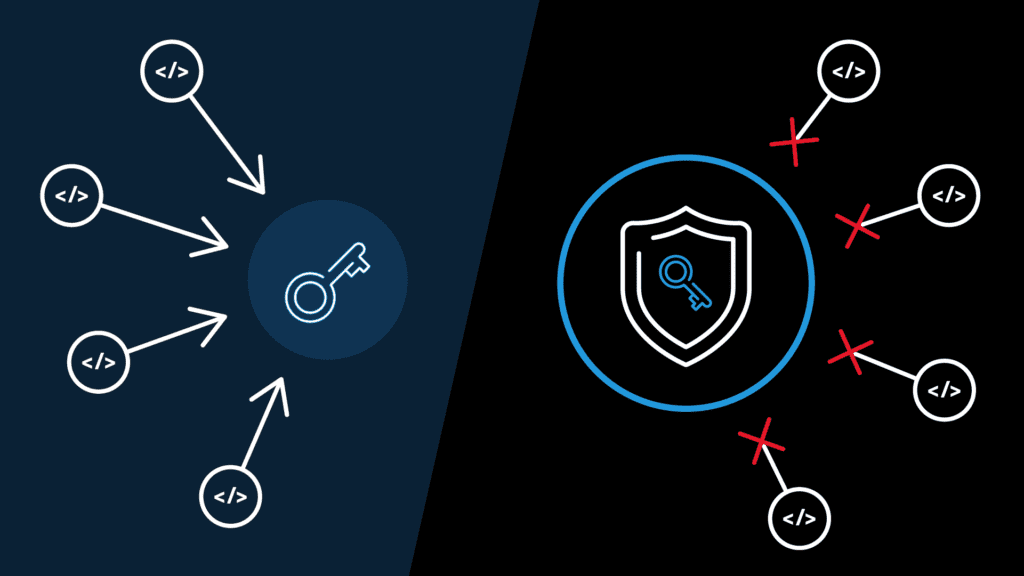
How to Manage Cloud Identity and Access Management Effectively
Cloud IAM involves managing access to cloud resources and services in a secure and efficient way. However, this is not an easy task, as there are many challenges that arise in Cloud IAM.

